Perhaps not surprisingly in the light of all the cyber-attacks and data breaches we’ve been seeing recently, the topics of cyber-security, cyber-resiliency, and securing one’s supply chains are at the forefront of our minds.
Several of my own columns have touched these topics in recent months, such as Yay! Finally! A Way to Secure the Supply Chain! and Cyber-Security’s So-So Soup; Cyber-Resiliency Rocks! and ID for the IoT? We Need the IDoT!
In fact, I was just chatting with Shahram Mossayebi, who is the CEO of Crypto Quantique. In turn, by some strange quirk of fate, Shahram had just finished reading my article on Infineon’s IDoT, saying, “That was spot on. Connectivity and the IoT are at the heart of so many things in today’s world and the number of connected devices is growing massively. The concept of identity becomes the key point in security.”
The thing is, when there are billions upon billions of connected devices in the world, how do you know if a device you or an application or a server are talking to is legit? In the same way that humans need to be identified for various purposes such as accessing different services, so too do devices need to be identified, but how is this to be achieved?
One technique is to embed unique ID numbers into the main integrated circuits (commonly referred to as “silicon chips”) used in a system — possibly in non-volatile memory — when those devices are fabricated. Another approach is to employ the concept of a physical unclonable function (PUF). This refers to a physical structure that is fabricated directly into the semiconductor material. For a given input under specified conditions (the “challenge”), the PUF will provide a physically-defined “digital fingerprint” output (the “response”) that can serve as a unique identifier.
The PUF concept, which has been around for quite some time now, is really rather interesting. The underlying mechanism is that when we fabricate silicon chips, although these chips may appear to be identical in form and function at the macroscopic level, there will be tiny process-induced variations at the microscopic level. Even chips created adjacent to each other on the same wafer, or transistors created next to each other on the same chip, will exhibit tiny differences at the quantum level, and it is these differences that can be used to form the basis for a PUF.
The idea is that we can use these subtle differences to give the chip an identity, but we first have to convert them into something in a form we can use. The PUF can’t just “squirt out” a series of quantum values. Instead, it has to use those values to generate a unique ID. So, as opposed to writing a unique ID into a component when it is fabricated, we now read out that component’s unique ID and associate it with the part from that point onward.
Like most things, of course, this is a lot easier said than done. For example, one form of PUF is based on creating a special small SRAM (or using a small portion of a larger general-purpose SRAM). This form of memory is volatile, which means it forgets its contents when power is removed from the system. Also, when power is reapplied to the system, the SRAM powers-up containing random 0s and 1s… or does it?
In reality, due to the aforementioned process variations, although many of the SRAM bits on a chip may power up randomly containing a 0 or a 1, some of the bits will have a tendency to power up containing a 0 the majority of the time, while others will have the inclination to power up containing a 1. Furthermore, the bits with a propensity to power up one way or the other will vary from chip to chip.
Of course, leaning one way or the other is different to being solidly one way or the other, so the PUF’s control logic has to take this into account. It also needs to account for the fact that things may change as a function of environmental conditions like voltage and temperature. Furthermore, things may alter over time as the device ages.
One really big aspect to this is that of entropy, which is defined as “a thermodynamic quantity representing the unavailability of a system’s thermal energy for conversion into mechanical work.” More appropriately for our purposes here, entropy is often interpreted as “the degree of disorder or randomness in the system.”
This leads us to the problem with using something like an SRAM as the foundation for a PUF. The point is that a memory is supposed to be a memory. It has been built to act like a memory, so it does not produce true randomness. The fact that its initial state the moment you turn it on is “random looking” is not on purpose and not truly random. For example, it may power up containing substantially more 0s than 1s, or vice versa. In order to achieve “the bestest random ever,” as Pooh Bear might say, it’s necessary for the PUF to provide the maximum possible entropy — because high entropy is the foundation for high security with regard to cryptography — which means the ratio of 0s and 1s need to be as close to 50:50 as possible.
Yet another consideration — one that many engineers don’t fully understand — is that not every random number is good for cryptography or security purposes. From a cryptographic point of view, not every “random looking” string is random enough — it has to be cryptographically random, as it were.
All of which leads us back to Crypto Quantique, which boasts a diverse engineering team from quantum physicists to cryptographers to analog chip designers to software developers, augmented with a crack commercial team coming from both the software enterprise and semiconductor industries.
What the folks at Crypto Quantique have done is to take a step back and come at this problem from a new direction, starting from scratch. By nature, quantum processes are inherently non-deterministic, which means they give the highest entropy. This is the point where Shahram started waffling on about quantum tunneling through gate oxides and observing the random quantum tunneling effects of transistors and how by comparing values from pairs of transistors you can create random bits and… I’m afraid I blacked out at this point.
When I eventually regained consciousness, it was to hear Shahram say something along the lines of: “Crypto Quantique’s QDID IP, which can be smaller than a traditional SRAM PUF, is compatible with any traditional CMOS process and comes in the form of a lattice [I’m thinking array] of these truly random bits that allows the chip to generate multiple identities of cryptographically random strings that are re-constructible inside the die.”
Further probing on my part revealed that one way to generate a cryptographic key would be to access a collection of bits from the array using a randomly generated sequence of X/Y coordinates. Another approach would be to simply read a column of bits from the array. If you want the same key, you read the same column — if you want a different key, you read a different column. After this, you can start to get a little crazy. For example, you could use one column of random bits as a seed for a linear-feedback shift register (LFSR), and then use that to pseudo-randomly select random bits out of the array. If you know a little bit of math and algebra, once you have a “pool of randomness,” you can use it to generate a larger pool of randomness. Basically, you can expand your “randomness space” and then sample from the bigger space rather than the smaller one.
Another thing about QDID IP is that you can configure it before you build it into your chip. You want 256-bit keys? No problem. You need uber-security based on 512-bit keys? No problem. You’re creating an IoT sensor with a very small die size and ultra-low power requirements and a small QDID block that generates only two keys will suffice? Again, no problem.
Furthermore, QDID IP is both flexible and scalable. Suppose that all the keys you’re currently generating are for RSA cryptography. That’s fine at the moment, but now suppose that your device is deployed in the field and — a few years from now — once NIST certification is in place for post-quantum cryptography, you find you need to generate post-quantum secure cryptographic keys for an LWE scheme, for example. If you lack the ability to adapt your cryptographic keys on the fly, you will need to change things, which may potentially require modifications to the device. By comparison, in a QDID IP-based scenario, you’ve got enough randomness and all the flexibility you need. All you have to do is change some parameters, and now, instead of generating your RSA key, you have sufficient randomness to generate an LWE key, for example.
Eeek! I almost forgot to mention that, for developers interested in minimizing the power consumption of their device, the QDID array is powered down most of the time, thereby consuming zero power. The moment you want a key, you simply enable the power for the specific column you wish to read for a fraction of a second, generate the key, and power-down the column again.
But wait, there’s more. A lot of PUF purveyors will sell you their IP and then run for the hills. Actually, that’s not strictly true, because they typically partner with one or more other companies to offer a comprehensive solution. On the other hand, it’s typically easier to work with a single supplier than with a bunch of them who are wont to point fingers at each other should things go pear-shaped. By comparison, the guys and gals at Crypto Quantique have created a true end-to-end solution that spans die-to-cloud.
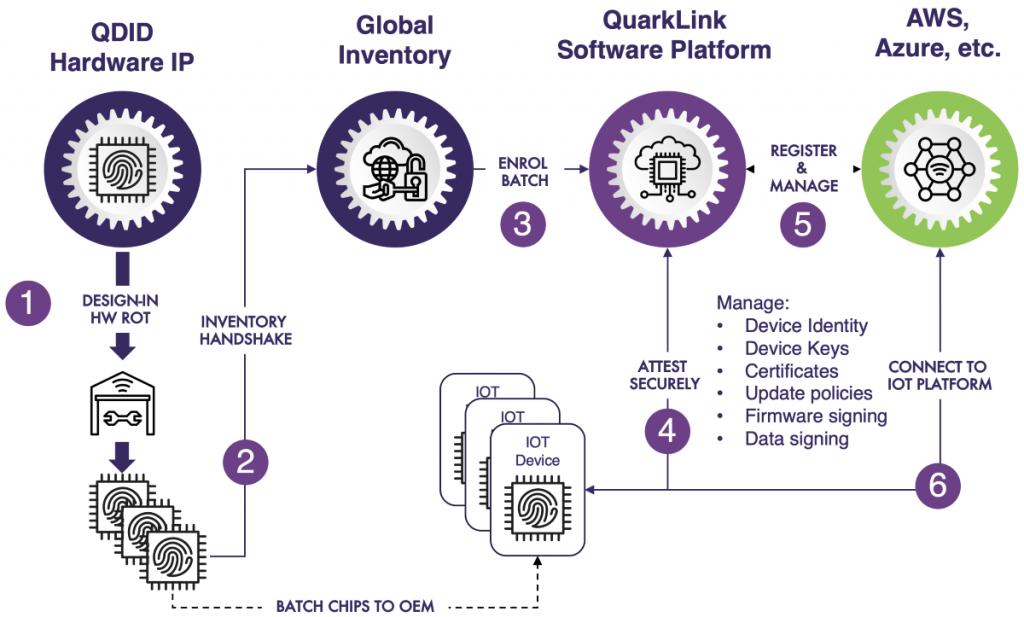
Scalable end-to-end security from die-to-cloud
(Image source: Crypto Quantique)
It’s rare to find a single company that understands — and offers a solution for — the entire security enchilada, including silicon security, software security, and cloud security. As Shahram told me:
In addition to our QDID Hardware IP we have our QuarkLink Software Platform. We provide the software and cloud services to make things seamless and easy for the end customer to use. We’ve solved the trust issue in the supply chain because we’ve come up with cryptographic protocols that alleviate the need for key injection in the supply chain and provide encrypted authenticated firmware for devices, so we don’t need to trust anybody in the supply chain for the provisioning of the devices. Also, our solution automates the onboarding process to any cloud service, such as Azure, AWS and others.
It does all of this without revealing any of the secrets belonging to the developers, the OEM, or any of the parties, including the cloud side. All of the data will be encrypted all the time, and neither we nor the cloud service provider will have access to any of the keys or be able to see the data. We’re basically putting developers and OEMs in full control of the security and privacy of their data.
All I know is that Crypto Quantique must be doing something right, because I understand that the majority of the world’s leading chip manufacturers are currently considering adding QuarkLink to their ecosystem. I also believe that Crypto Quantique is poised to double in size by the end of 2021 and there are plans to open offices in Japan and in the USA.
As a closing thought, I’m sure we’re all conversant with the quantum mechanical thought experiment known as Schrödinger’s cat, which illustrates a paradox of quantum superposition. In this thought experiment, a hypothetical cat may be considered to be simultaneously both alive and dead as a result of being linked to a random subatomic event that may or may not occur. Well, based on Crypto Quantique’s quantum PUFs, from the Industrial IoT (IIoT) perspective, it’s interesting to think that a metaphorical cat (widely acknowledged to be the best sort) may soon take over from guard dogs in securing industrial assets.*
(*To be honest, my chum Bob Jones, who is the founder of Originality B2B, came up with this quantum quip, but I simply couldn’t restrain myself from using it here. Also, just seconds before “going to press,” as it were, in a strange specimen of synchronicity, my chum Jay Dowling just sent me a link to an IEEE Spectrum article describing how Amazon’s New Quantum Computer Design Relies on Tiny Schrödinger’s Cats.)






Hi Max, another really interesting article – thank you. I shall be watching how this company and technology/devices evolve. What I really need now is a very strong black coffe and a sit down!