When most people hear the term “counterfeiting,” their knee-jerk reaction is to think of currency, the counterfeiting of which is as old as the concept of money itself. Around 400 BC, for example, metal coins in Greece were often counterfeited by covering a cheap-and-cheerful material with a thin layer of a more precious metal.
Or take the original American colonies. Throughout northeastern America, Native Americans would employ shell beads known as wampum as a form of currency. White shells came from quahog (a large, rounded edible clam found on the Atlantic coast of North America), while blueish/purplish-black shells came from certain types of whelks (sea snails). Since the blueish/purplish-black shells were rarer, they were perceived as having a higher value. It wasn’t long before wayward traders started dipping white shells in a blueish/purplish-black dye and passing them off as the more expensive items.
In reality, counterfeiting has probably been practiced as long as people have been able to articulate something along the lines of: “Of course this isn’t a common long-haired sheep — it’s an extremely rare cross between an Arapawa, a Beltex, a Najdi, and a Zwartbles — it’s the only one of its kind — almost a family heirloom — I couldn’t possibly accept anything less than two cows and three goats for this little beauty!”
The higher the stakes, the greater the incentive to counterfeit something. Even if I won the lottery, I’d be reluctant to invest in a hitherto undocumented early rendition of the Mona Lisa that someone I met on my travels claimed to have found in his attic, for example. On the bright side, when I was young, counterfeiting was not too much of a problem for people in our circle and circumstance. Although we were a happy bunch, my family didn’t have a lot of money, and what we did have left over as disposable cash we mostly spend on food at the local greengrocer, butcher, and fishmonger (when that man monged a fish, it knew it had been monged, by golly). Unless your audience is overly susceptible, or you are a virtuoso at sleight-of-hand, it’s a tad tricky to pass off a cluster of carrots as a passel of parsnips, for example.
Like most of us, as I’ve grown older, I’ve been exposed to counterfeit products. Once, whilst ambling around in Hong Kong circa the mid-1980s, I was approached in the street by someone asking if I was interested in purchasing a genuine fake Rolex. I wasn’t, but I had to admire the “genuine fake” portion of the portrayal. A few years later, while presenting a paper in Singapore, a friend took me to a small backstreet shop he knew, where he said I could purchase some cheap jeans. After I’d found a couple of pairs I liked, I took them to the checkout, which was comprised of a little old man sitting on a stool next to a wooden desk upon which resided a cash machine and a sewing machine. When this wizened gentleman asked me what sort of jeans I preferred, I assumed he was just making polite conversation and I responded that I was partial to Levi 501s. He immediately whipped open a drawer under the counter, removed two Levi 501 labels from one of numerous compartments, and sewed them into the jeans before I could think of anything to say (which isn’t like me).
As an aside, my grandfather was part of the team that charted Singapore Harbor using rowing boats, surveying equipment, and weighted lines (to measure the depth of the water), and he was also in the party that charted Borneo to create the first credible map of the area (see also The Times They Are a-Changin’). I wonder what he would have thought if he’d been informed that his favorite grandson would one day be strolling the streets of Singapore clad in counterfeit jeans, but we digress…
Amusing (or rambling) stories aside, counterfeit products can produce very bad outcomes. One aspect of this is to impact a company’s revenue stream and damage that company’s reputation. Earlier, I noted that “The higher the stakes, the greater the incentive to counterfeit something,” and I mentioned the Mona Lisa as an example, but — rather than counterfeit one incredibly expensive item — counterfeiters are also more than happy to generate fakes of large numbers of lower-priced articles.
Take printer ink cartridges, for example. If you purchase a half-price unit from a shady-looking man in a bar, and that unit’s package flaunts a skull-and-crossbones accompanied by a legend along the lines of “Weasel & Sons, Purveyors of Printer Ink to the Aristocracy,” then you will probably accept your part in any ensuing fiasco should things go pear-shaped. On the other hand, if you visit a reputable store and purchase a full-cost printer cartridge that purports to have been produced by HP (I use this company as an example only because this happens to reflect the printer on my desk), and if that cartridge is counterfeit and contains sub-standard ink, and if that sub-standard ink ends up “gumming up the works,” as it were, then — if you honestly believe that the cartridge is an HP original — your impression of that company will be negatively impacted, which may cause you to express your contempt to your companions, and which may well have long-term ramifications with regard to any future purchases on your part.
And, of course, things can get much, much worse. We could be talking about anything from counterfeit water filter cartridges that don’t perform the desired filtration functions or that allow pathogens to grow inside them, to counterfeit inhaler cartridges that contain too much or too little (or none at all) of the active ingredients, thereby impacting the user’s health, to counterfeit chargers that may under-charge or over-charge devices like smartphones and tablet computers with the potential of some part of the system spontaneously combusting.
Sometimes I fear that there are so many bad guys doing so many bad things that the rest of us don’t have a chance. And then I see a little flicker of light that gives me hope. For example, I was just chatting with Timo Grassmann (IFAG CSS ESS DA APK) from Infineon (I dare to counter Timo’s over-enthusiastic surfeit of qualifications with my own GMMS — “Grand Master of the Mystic Sprout”).
Timo was telling me about Infineon’s OPTIGA Authenticate IDoT, which was launched at the recent Embedded World 2021 Conference and Exhibition.
Described as a “Best-in-class, anti-counterfeit turnkey solution, combining enhanced device authentication with unprecedented levels of configuration flexibility,” OPTIGA Authenticate IDoT is comprised of both hardware and software elements. First, we have a small hardware chip containing a private cryptographic key that will reside in the consumable portion of the product (printer ink cartridge, inhaler cartridge, water filter cartridge, etc.).
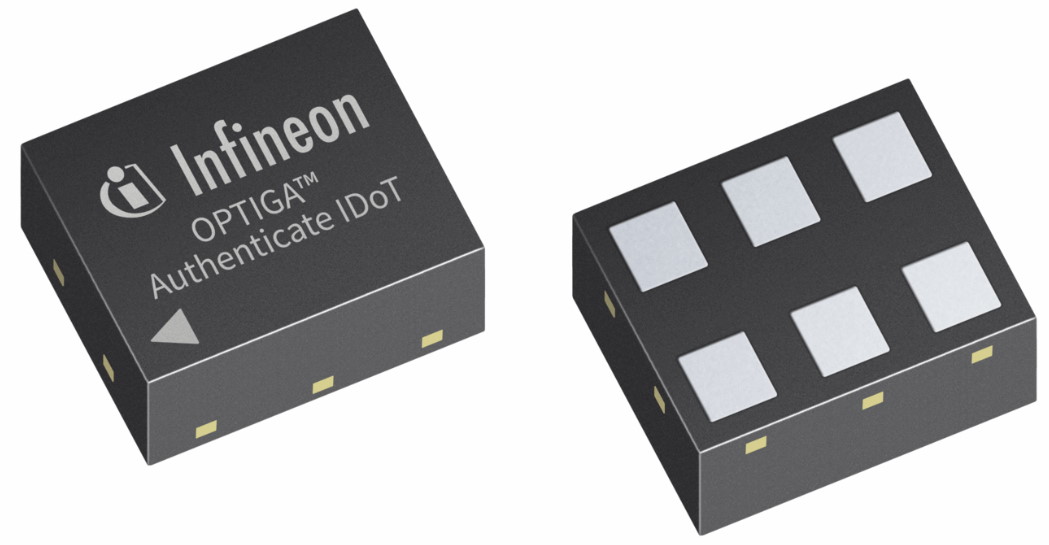
OPTIGA Authenticate IDoT chip (Image source: Infineon)
Happily, this image is not to scale, otherwise we would need substantially larger pockets to hold our inhalers. In reality, this little scamp is just 1.5 x 1.5 x 0.38 mm in size, boasts 8kV IEC61000-4-2 ESD protection, and is available in a variety of temperature options (-40 to +85°C, -40 to +105°C, and -40 to +120°C).
In addition to a unique 96-bit identifier (UID), these little beauties support 163-bit key Elliptic Curve Cryptography (ECC), four integrated lifecycle counters with independent End-of-Life (EoL) structures, options for 1Kbit, 2Kbit, and 5Kbit Secure Lockable non-volatile memory (NVM), and two serial communication options (SWI and I2C + GPO).
The keys, counter values, and other software elements are preloaded into the chips before they leave the factory. With regard to the counters, these can be used for a variety of tasks, such as limiting the number of times a water filter can be used, for example. The reason for maintaining the counters in the chips rather than on the host system is in case the consumable portion of the product is moved from one host to another.
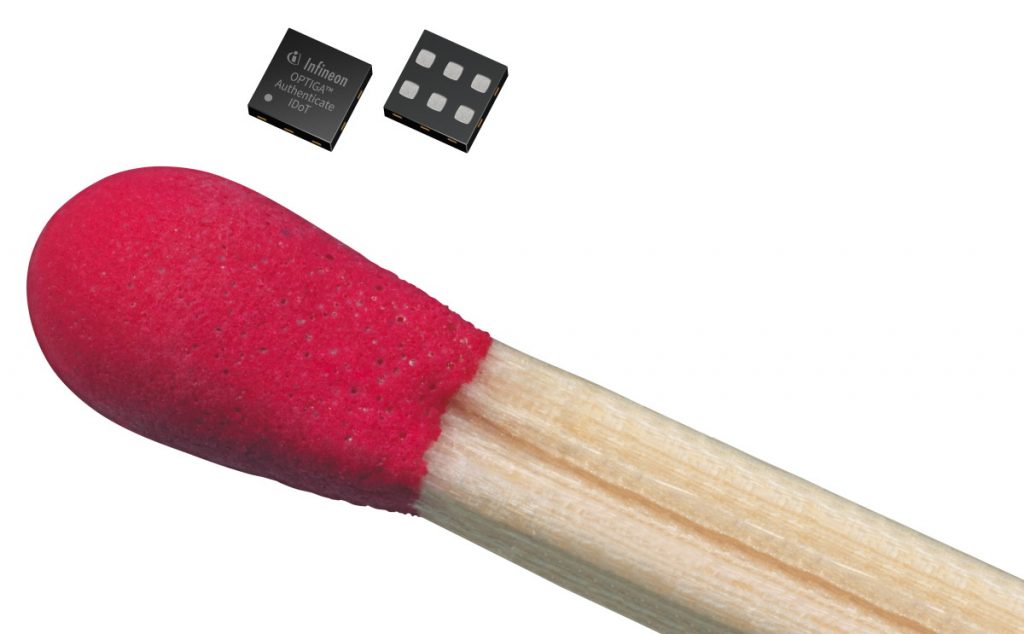
The IDoT chip is going to set the security world on fire (Image source: Infineon)
And, speaking of the host system, this is where the software containing the corresponding public cryptographic key resides. Every time the user attempts to access the product, the host system sends a challenge to the chip in the consumable portion of the product. If the chip responds appropriately and passes the test, everything works as expected; otherwise, the host informs the user that the consumable portion of the product is not to be trusted or employed.
The host system works with any microcontroller. Infineon provides a C library that you can use as the basis to implement whatever additional functionality you require, such as limiting the number of times the consumable portion of the product can be used or what to do if a counterfeit product is detected, for example.
To be honest, I long for a simpler life and a simpler world where we could all just get along and trust each other. A world without passwords and security certificates and cryptographic keys. A world in which we could happily create fun and interesting devices and connect them to the IoT without fear that some nefarious scoundrel might take them over and use them to our disadvantage. However, since we don’t live in such a world, we do need some way to verify and validate the identity of things (IDoT), so Infineon’s OPTIGA Authenticate IDoT is a very welcome addition to the party. How about you? Do you have any thoughts you’d care to share about any of this?






Hi Max, As usual a relevant and timely article. If anyone thinks “we can’t become a victim of cloning”, some years ago when vehicle telematics was young, imagine the surprise in the company where I worked when we found a unit for sale that looked and worked just like the one we had developed! These days, I wouldn’t think of putting a product on the market with something like the IDoT in it. (Other manufacturers/products are available!)
“These days, I wouldn’t think of putting a product on the market with something like the IDoT in it.”
“With”? I think you meant to say “I wouldn’t think of putting a product on the market WITHOUT something like the IDoT in it.” LOL
That would be pointless – because the cloned product would be built without IDot. This only has value is preventing counterfeit consumables and/or preventing the substitution of subassemblies.
So not only can you not use anything but an Official HP printer cartridge for your HP printer (even if you knew you were buying aftermarket) but also your Apple computer can’t be upgraded without Official Apple memory and Official Apple hard drives… Or better yet, your computer can’t be upgraded at all – throw it away and buy a new one! Capitalism at its finest.
Aaaaaarghh! Did I really say WITH! Of course I obviously meant WITHOUT! Thanks Max. Well spotted – fat fingers on the keyboard moment! We currently use a device from the Maxim family of secure authenticators. The packaging isn’t as small as the IDoT but on our board that isn’t an issue. What IS the issue is that the CPU can’t “pass GO” without consulting the Maxim device. Does anybody remember the Dallas 1-wire device with a unique 64-bit key! I recall that this was the first entry into this field that I had come across and the announcement from Dallas came at the right moment because the telematics device I was working on back then had just become the victim of a clone (see above)! Having been bitten and having a solution in the form of the 1-wire device that could uniquely fingerprint every PCB that the company made made me aware that this was the future! Sad but true. I like the look of the iDoT but haven’t yet seen it announced anywhere else and so time for a bit of further digging! The device that we are using has its own on-chip security features but the Maxim/IDoT allows us to fingerprint the PCB on which that device sits. Overkill! I don’t think so. Thanks again Max – well-timed -well-written.
Okay – fat fingers here again. Never one to waste the opportunity to download a datasheet – short form now residing in my security products folder. I am more used to seeing Infineon in the automtive market where they have an ethos of robustness and reliability. I have used their MCU offerings in products destined for environments where “failure is not an option”. One of the points that my eye was drawn to in the article was the available temperature range and ESD rating. I didn’t attend the (virtual) event where this was announced and so would have missed this without seeing this article. The regular emails I get from EE Journal are required reading!
Unfortunately, this is all too likely to be used in ways to eliminate the ability for consumers to have devices repaired. The hard drive from a MacBook with a damaged logic board won’t be usable in a different MacBook with a bad drive because the “id doesn’t match”.
Individual IDs for items are designed to prevent subcomponents from being re-used, even if they’re still good. The analogy to water filters is cute, but the primary value of this is that it not only prevents counterfeiting but it also eliminates competition and enforces obsolescence.
This reads like a nightmare product for those of us concerned with “Right to Repair”.
Hi Chuck, I also believe in the “right to repair” but as with all technologies it is all about how you use the technology. If you buy a product from me – it is your product and belongs to no-one else. I have a smartphone, which although I paid for it, really belongs to Google or least Google thinks it does! I have very little control over the function of the phone and when it decides it wants to “upgrade” it software – it does. We use the Maxim device like a set of house keys but if you want to put your own software on it – feel free – you have a CPU core all of your own to play with. We can even give you your own set of house-keys! Not even we will be able to break into your house! If we find a security bug in the code resident on your device that we provided we will make a fix available. But wait! How do you know it really us and not some malcontent? If the key fits the lock then go ahead and install the fix – confident that it really is a genuine fix from us. Ransomware? I have an Internet MODEM/router from a very reputable company that was rendered useless by being cracked. It is languishing in a pile of stuff to be fixed when I can find the time. I am actually hoping that I can find a JTAG header on the PCB somewhere! The attack would not have succeeded with proper access control. Some miscreant tampered with the code on a router that I paid for! Not here! I could rant on but won’t! I felt that your post needed a reply that addresses a very legitimate concern.
RedBarn, I agree that companies need to overhaul their “software supply chain” so that upgrades are safe and from trusted sources but that’s not the market this device serves. Your internet Modem is a great example – unless you expect that updates will be delivered in physical form like a USB drive, then there’s nothing “containing the chip” for the modem to validate against. The fact of life is that is that fixing vulnerabilities isn’t profitable the way that eliminating competition is:
https://www.industryanalysts.com/72920-etira/
I disagree with you about devices coming with automatic updates turned on – that needs to be a fact of life for anything connected to the internet. We can’t wait or depend on end users to click a button or manually download some update before a device gets a security fix, or worse provide no way to update the device. I have no problem with people being able to opt-out of automatic updates, but the default should be to opt-in. Otherwise the internet will cease to function as bigger and bigger botnets are created with, and more fraud takes place as phones are hacked.
I think that buying a phone from Google instead of one from Verizon/ATT/T-Mobile where Google promptly gets the security updates out is a lot smarter than buying one where the security updates have to trickle through your service provider so you wander around with an insecure phone for longer.
Finally – this chip isn’t a panacea. If you use this chip to release security updates for your “Maxim device”, unless you know what you’re doing all the hacker has to do is do the same and clone the contents of the chip’s memory. (Assuming your Maxim device can do HMAC, you can create a hash of the “update binary” and store a hash message with HMAC in the chip. If your hash algorithm is strong, no problem, but if you just grabbed SHA1 off the shelf an attacker’s going to be able to generate his own updates.)
A last caution – this chip is really designed for consumables, if you’re ok with creating “security update keys” just for your customer to toss them into a landfill once used, you might want to re-visit your sustainability model.