Security researchers have refined a long-theoretical profiling technique into a highly practical attack that poses a threat to Tor users and anyone else who wants to shield their identity online.
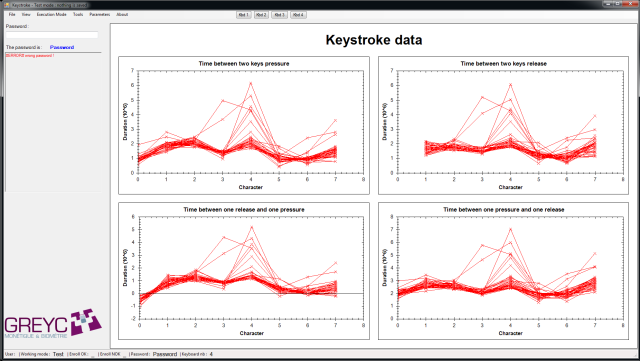
The technique collects user keystrokes as an individual enters usernames, passwords, and other data into a website. After a training session that typically takes less than 10 minutes, the website—or any other site connected to the website—can then determine with a high degree of certainty when the same individual is conducting subsequent online sessions. The profiling works by measuring the minute differences in the way each person presses keys on computer keyboards. Since the pauses between keystrokes and the precise length of time each key is pressed are unique for each person, the profiles act as a sort of digital fingerprint that can betray its owner’s identity.
via Ars Technica




