Today, it’s all about trust. Whom do you trust? And what is it about them that makes you think that they’re trustworthy? With people, it’s about knowing them and their intentions – more on that in a minute, but it’s a bit different with machines.
The IIC’s Take
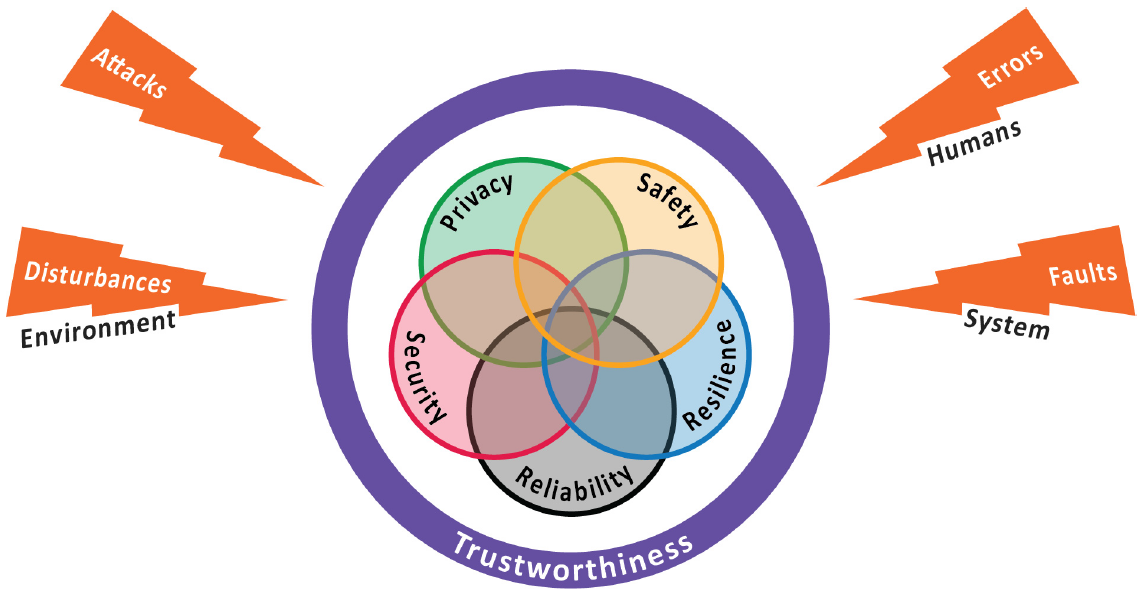
The Industrial Internet Consortium (IIC) put out a document that takes something as fuzzy as trustworthiness and pins it down into something more formal. They define trustworthiness as the “degree of confidence one has that the system performs as expected with characteristics including safety, security, privacy, reliability and resilience in the face of environmental disturbances, human errors, system faults and attacks.”¹
(Click to enlarge. Image courtesy the IIC.)
So they see five aspects of a machine that establish its trustworthiness. They define them as follows:
- Safety: “the condition of the system operating without causing unacceptable risk of physical injury or damage to the health of people, either directly, or indirectly as a result of damage to property or to the environment (adapted from ISO/IEC Guide 55:1999, modified for consistency).”
- Security: “the property of being protected from unintended or unauthorized access, change or destruction. Security concerns equipment, systems and information, ensuring availability, integrity and confidentiality of information.”
- Privacy: “the right of individuals to control or influence what information related to them may be collected and stored and by whom and to whom that information may be disclosed (original from ISO TS 17574:2009).”
- Reliability: “the ability of a system or component to perform its required functions under stated conditions for a specified period of time (original from ISO/IEC 27040:2015). This includes expected levels of performance, QoS, functional availability and accuracy.”
- Resilience: “the ability of a system or component to maintain an acceptable level of service in the face of disruption. This includes the ability to recover lost capacity in a timely manner (using a more or less automated procedure), or to reassign workloads and functions.”
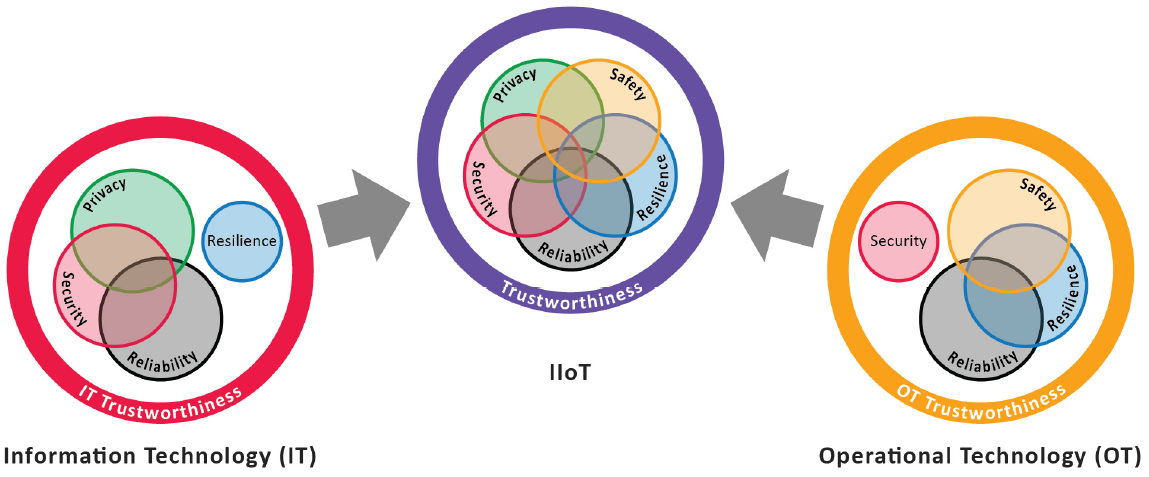
Because we’re talking about the industrial internet of things (IIoT) here, they also relate the five to the notions of operational technology (OT) and information technology (IT). You’re probably familiar with the IT aspect; the OT part deals with the technology on the shop floor that makes things happen. They see safety and resilience as largely OT concerns. Security applies both to OT and IT, but the OT aspect of it is more with physical security and human access; the IT aspect of it deals with the notions of information security that we’ve been following. Reliability is also a concern shared by IT and OT, while privacy is largely an IT thing.
(Click to enlarge. Image courtesy the IIC.)
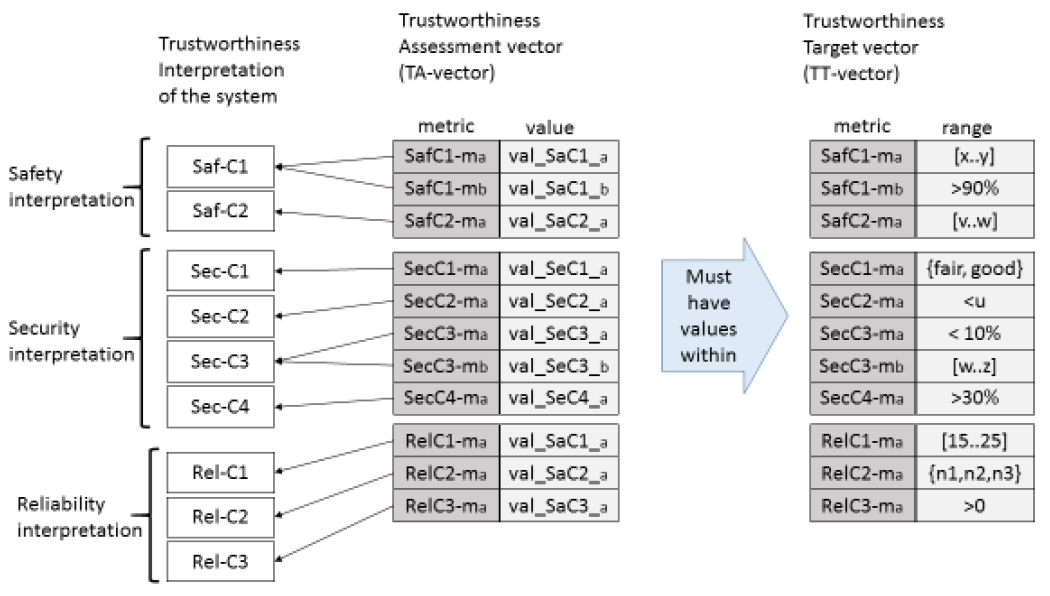
Of course, for the IIC, it’s all about setting policy and then measuring where organizations stand as compared to that policy. So, for each of the five components, you set a desired range, and then you assess where on that scale a specific system falls. Generically, the attributes feel a bit squishy to me, so quantifying both targets and actual values would presumably take some definition work. The IIC shows one way of expressing both the targets and assessments as vectors. The following image reflects vectors for a system that isn’t concerned about the resilience or privacy factors – such as what they call a Factory Operations Visibility and Intelligence (FOVI) system.
(Click to enlarge. Image courtesy the IIC.)
They provide a couple of alternative ways of viewing the trustworthiness of such systems, one of which is a spatial view, which is quantitative.
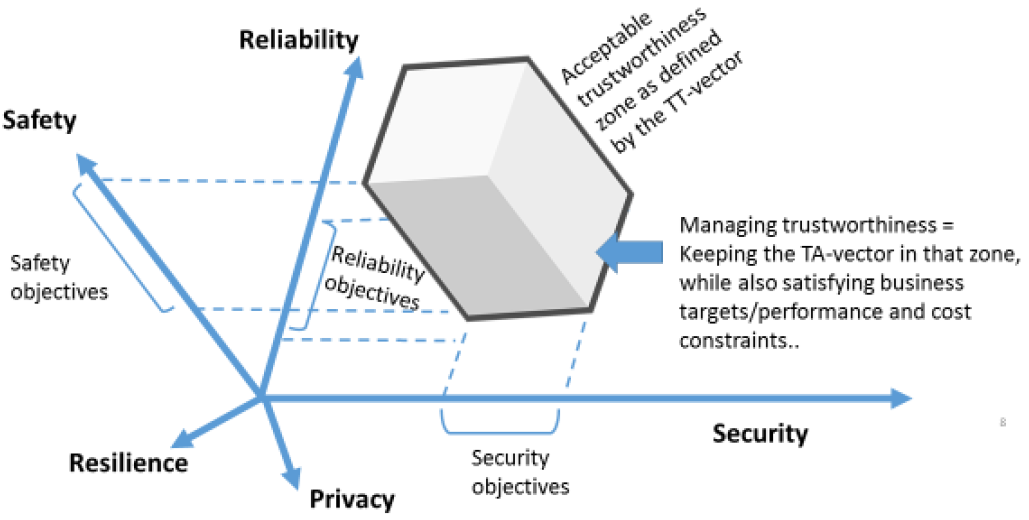
(Image courtesy the IIC.)
The other alternative is a spider diagram, which is based on quantitative results, but gives a more qualitative impression.
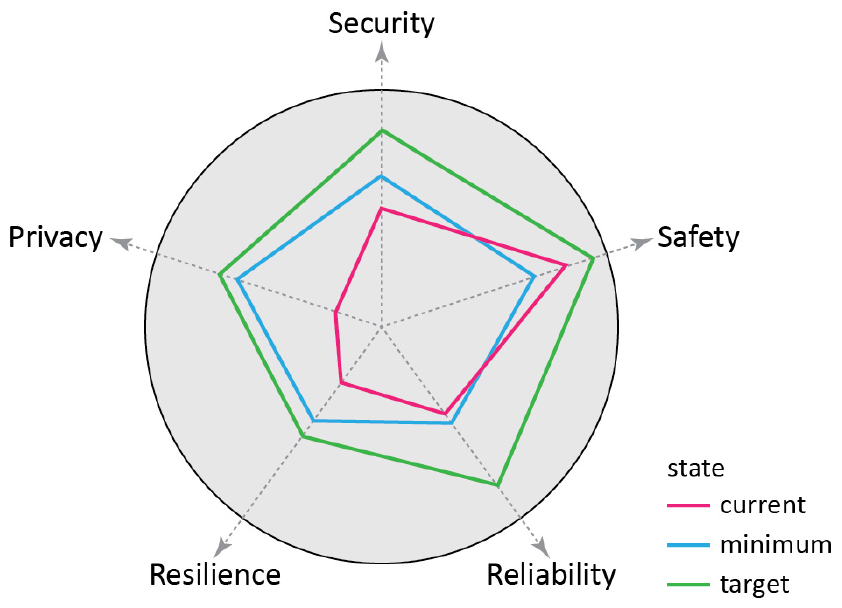
(Image courtesy the IIC.)
Beyond that, they go into lots of detail on creating policy and setting goals, as well as making assessments. If this is something you’re tasked with tackling, then it’s likely to be a useful read (link is below).
Welcome to the City of Osmio??
Meanwhile, we leave machines and come back to people. And what we cover next had me confused for a while. I had a conversation with the CEO of what’s called The Authenticity Institute. And in that discussion, he referred me to, among other places, a website for a city named Osmio. The website has a .ch top-level domain, suggesting that this city is in Switzerland. And yet I would be able to acquire credentials and such from that city – without being a resident. What the heck?
A quick Google Maps check found Osmio to be… nowhere.
So, to save you some confusion and trouble: no, Osmio isn’t a real city. (I couldn’t find a definitive statement to that effect easily visible on the website.) So, with that out of the way, let’s back up and figure out what’s going on here.
The Authenticity Institute bases its work on the idea that we really can’t tell who people are. Yeah, we have the public-key infrastructure (PKI), which relies on certificates of authenticity to vouch for our… authenticity. Their concern is that it’s easy to fake the systems and get a certificate that’s not rooted in reality.
So they take the notion much further, expanding it in different directions to cover a number of different aspects of our interactions, scoring each of them and creating an IDentity [sic] Quality Assurance, or IDQA, score. There are 8 factors, each scored 0-9 for a possible total of 72. But there’s no right or wrong score; the breakdown is intended to allow different entities to assess different characteristics, according to what’s important to them.
From their site, as an example, “a seller in a multimillion-dollar real estate deal might require the buyer to have a high score on Metric 7 (assumption of liability) to protect against a fraudulent transaction, but a chat room for young girls might require a high Metric 2 score [rigor of enrollment methods] that ensures face-to-face enrollment, to protect against child predators joining the room.”
The eight metrics for an authenticity credential are as follows:
- “Degree of protection of personal assets,” or “skin in the game” from the individual, not their organization.
- “Quality of enrollment practices,” where, for example, face-to-face scores higher than online.
- “Quality of means of assertion,” checking whether credentials follow various well-known standards.
- “Quality of authoritative attestation” – basically, what authority is vouching for you.
- “Self-sovereign EOI [Evidence of Identity] and attestation from others,” which seems pretty much like an assessment of how many other reliable sources around you will vouch for you.
- “Quality of the credential,” as in the number of keys or key pairs or authentication factors, etc.
- ”Quality of assumption of liability” – if something goes wrong, who’s liable? The person? An insurance policy or a bond?
- “Reputation of the credential,” which gets to how long the credential has been used with no reports of any adverse incident (like revocation).
Enrollment in a system like this can be done at the City of Osmio, which, as we noted above, is virtual. In fact, not only is it not a city, but it’s more or less a certificate authority (CA) for this new approach to authenticity. There’s a fair bit of infrastructure that’s been put together to support this, although it certainly hasn’t been particularly visible – at least to my eye.
There’s a ton to study here, but it’s not helped by the fact that, first, you have to figure out whether this Osmio thing is a literal city or not. And the materials are scattered over various different websites like osmio.ch, attestation.pro, whatisPKI.com, and authenti-share.com – to name a few. And they do things like redefining PKI to something else while giving what we call PKI yet another TLA.
Then there’s the “Quiet Enjoyment Index,” whose role isn’t clearly described – at least not where I was looking. It appears linked to the legal definition of quiet enjoyment, but there are lots of notions like that that may be obvious to specialists, but that required a lot of background for me.
So I did find myself somewhat tied into mental knots, wondering how real this whole thing is.
Real or not, there are lots of interesting ideas to consider in the readings that are available, so there is certainly value in taking the discussion out of the realm of specialists and bringing them to a broader audience. Whether this does, in fact, represent the future of our digital authenticity has yet to be proven.
Notes:
- The Industrial Internet of Things Volume G8: Vocabulary; https://www.iiconsortium.org/pdf/IIC_Vocab_Technical_Report_2.1.pdf
More info:
The Industrial Internet of Things: Managing and Assessing Trustworthiness for IIoT in Practice
Sourcing credit:
Wes Kussmaul, President and CEO of The Authenticity Institute






What do you think of these approaches to digital trustworthiness?