I love all of the cool things that today’s incredible technologies make available to us. Take the internet, for example. I think it’s fair to say that I avail myself of the awesome access it provides to information from dawn to dusk. Even when I’m relaxing in the evening watching a program on the television, I’ll be using my trusty iPad Pro to look up information on actors, locations, unfamiliar words… all sorts of things.
I remember when I commenced my career in the early 1980s. At that time, gaining access to information was a non-trivial task. Every engineer had his or her own little “library” of data books in their office (I still have my trusty orange-yellow Texas Instruments TTL data book — which was an invaluable resource in those days of yore — here in my office).
Companies used to give their engineers a yearly stipend for magazine subscriptions and data book purchases. If you worked for a big enough company, it might even have its own small library. If you needed a data book you didn’t have, it could take a couple of weeks to write to the manufacturer and for them to respond. Yet another source of information was the data sheets and application notes provided by the representatives from local component distributors.
Now, this was all well and good if you knew what you were looking for, but such was not always the case. Circa the early 1980s, I spent some time writing functional test programs for printed circuit boards (PCBs) that had been created by other companies. In order to do this, I was provided with what was claimed to be a known good board (it often wasn’t) and a schematic diagram whose version was supposed to match that of the board (it often didn’t). I remember receiving one such unit (part of an aircraft navigation system) and finding a large, strange, 1.5” x 1/5” package with unfamiliar markings mounted in the middle of the board. It took us quite some time to determine that this was in fact an 8 x 8 magnetic core memory array, and several weeks more to obtain a data sheet for the little rascal.
Today, by comparison, all I would have to do would be to enter this device’s markings into Google to be provided with access to more information than I knew what to do with.
And it’s not just the internet with which I am enamored — it’s everything that goes with it. Smartphones, smart speakers, tablet computers, smart appliances, smart homes, wireless networks, cellular networks, satellite networks — I love it all. But… at the same time… there’s a fly in the soup and an elephant in the room (I never metaphor I didn’t like), which is the topic of security.
I dream of a world where engineers could focus on creating cool stuff without having to give any thought to nefarious scoundrels mounting cyberattacks to steal, corrupt, delete, or ransom our precious data and/or to subvert or destroy our systems. Unfortunately, we don’t live in such a world. Instead, we are surrounded by cybercriminals in the form of individuals, groups, and nation states who wish us naught but harm, thereby obliging us to design our systems from the ground up with cyber security and cyber resiliency in mind.
As defined by the National Institute of Standards and Technology (NIST) in special publication SP 800 193, platform firmware resiliency (PFR) involves protection, detection, and recovery. Protection includes protecting the platform’s firmware and critical data from corruption and ensuring the authenticity and integrity of any firmware updates. Detection includes cryptographically detecting corrupted platform firmware and critical data when the system is first powered on, while the system is running, and following any in-system updates. Recovery includes initiating a trusted recovery process and restoring any corrupted platform firmware and critical data to its previous value.
A Root of Trust (RoT) is a source that can always be trusted within a cryptographic system. It’s the foundation upon which all secure operations of an electronic system (computing, networking…) depend. And what is it that brought the topic of RoTs to the forefront of my mind? Well, I’m glad you asked. I was just chatting with the chaps and chapesses at Microchip Technology, who are very excited to be launching the fifth generation of their RoT controllers. This new generation of devices is known as the CEC173x Trust Shield family.
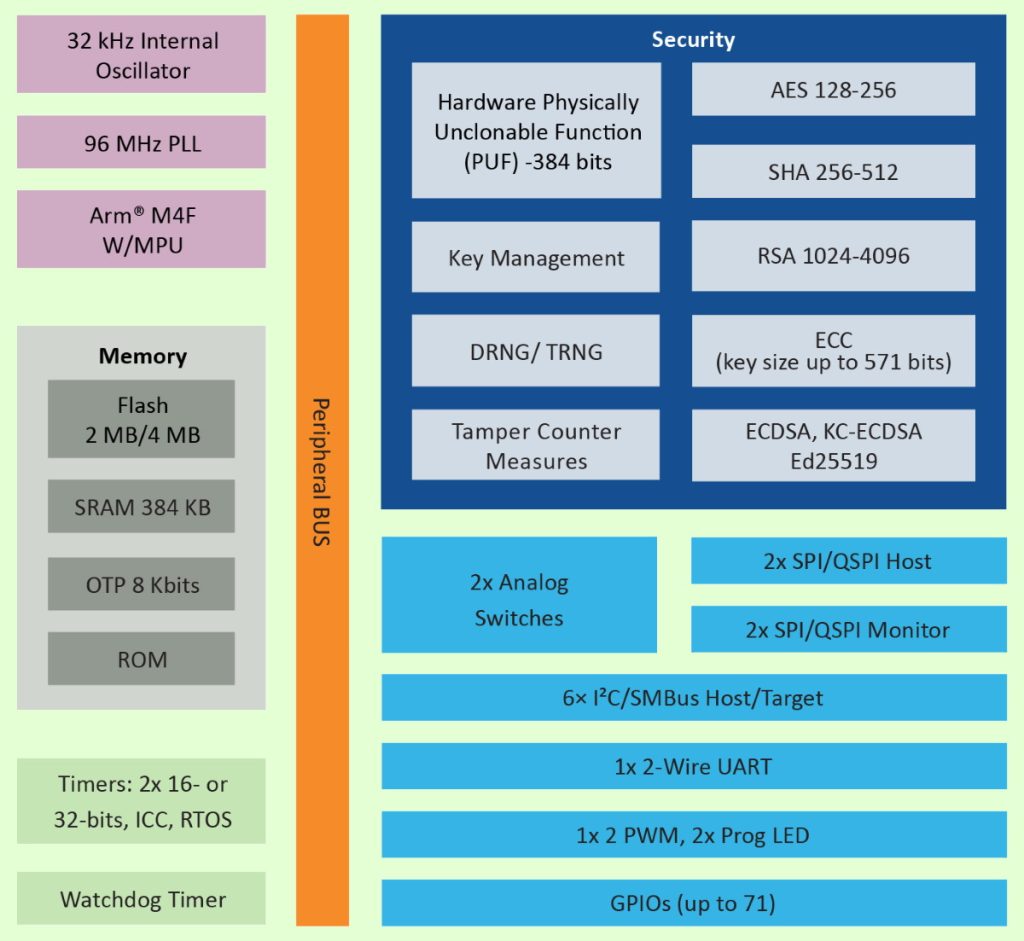
CEC173x Trust Shield block diagram (Image source: Microchip)
The idea here is that, as the market need for security evolves, platforms must also evolve quickly to defend against cyberattacks during start-up, real-time, and system updates. With these new market threats, designers cannot assume that the equipment they are using is trustworthy and they must start looking to new technology to secure their systems.
The fully configurable, microcontroller-based CEC173x Trust Shield family addresses these challenges by going beyond NIST 800-193 Platform Firmware Resiliency guidelines with runtime firmware protection that anchors the secure boot process while establishing an entire chain of trust for the system platform.
CEC173x Trust Shield enables runtime firmware protection in the SPI Flash and I2C/SMBus filtering against runtime attacks. The attestation feature provides trustworthy evidence to ensure that critical devices in the platform are authentic. Lifecycle management and ownership transfer features protect secrets throughout the product lifecycle and during the transfer of product ownership, allowing different operators to use the system platform securely without compromising information.
The CEC173x Trust Shield family’s advanced hardware crypto cipher suite is equipped with AES-256, SHA-512, RSA-4096, ECC with a key size up to 571 bits, and an Elliptic Curve Digital Signature Algorithm (ECDSA) with a 384-bit key length. The 384-bit hardware Physically Unclonable Function (PUF) enables a unique root key, symmetric secret, private key generation and protection. This advanced RoT and security solution, which meets the NIST 800-193 and OCP security guidelines, allows for a quick adoption of the latest security advances and standards.
Microchip’s CEC1736 Trust Shield solution spans silicon, software, tools, a CEC1736 Development Board, and provisioning capabilities that drive end-to-end platform firmware protection.
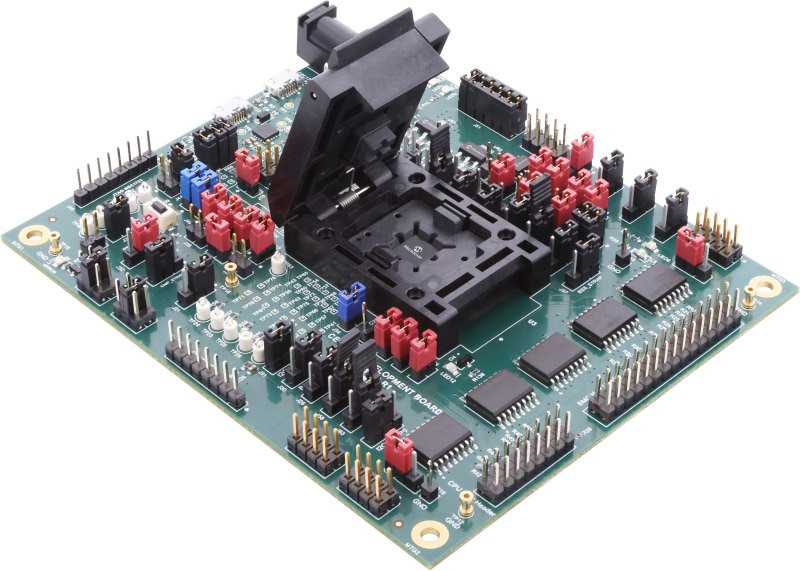
The CEC1736 Development Board (Image source: Microchip)
The CEC1736 Development Board (EV19K07A) comes equipped with out-of-the-box demos employing a pre-provisioned CEC1736, application processor emulation, on-board 4x flash devices (128 MByte), a CEC1736 socket, a BMC host header (I2C, QSPI, GPIOs), a CPU host header (QSPI, GPIOs), and a programming/debugging interface.
Microchip’s easy-to-use development tools for the CEC1736 Trust Shield family start with the Trust Platform Design Suite (TPDS), which boasts a Graphical User Interface (GUI) configurator for exploring capabilities, defining the security configuration, and provisioning secrets for prototyping and production. Meanwhile, Microchip’s MPLAB Harmony is a fully integrated embedded software development framework that simplifies device setup, library selection, and application development. And all of this is accompanied by training webinars, videos, and user guides.
As I discussed when opening this column, I long for a world in which we could trust everyone, and I hate that we even have to think about protecting our systems from cybercriminals. Having said this, since we live in the real world and are wading up to our armpits in cyberslime, it makes me feel a little better to know that the folks at companies like Microchip have our backs with products like their CEC173x Trust Shield family. What say you? Do you have any thoughts you’d care to share on anything related to cyber security, cyber resiliency and cyberslime?





