In just a moment we are going to cogitate and ruminate over the question of how to secure our RISC-V-based systems, but first…
Deep in the mists of time in that awesome decade we used to call the 1970s, although I was in my teens and many exciting things were occurring to capture my attention, I still remember my excitement when 8-bit microprocessors began to arrive on the scene. This started in November 1972 with the Intel 8008, which was essentially an 8-bit version of the 4-bit 4004. Containing approximately 3,300 transistors, the 8008 was the first microprocessor to be supported by a high-level language compiler called PL/M.
If the truth be told, the 8008 (like the 4004 and 4040) was designed for a specific application, and it was not until April 1974 that Intel presented the first true general-purpose microprocessor, the 8080. This 8-bit device, which contained around 4,500 transistors and could perform 200,000 operations per second, was destined for fame as the central processor of many of the early home computers.
Following the 8080, the 8-bit microprocessor field exploded with devices such as the 6800 from Motorola in August 1974, the 6502 from MOS Technology in 1975, and the Z80 from Zilog in 1976 (to name but a few).
And then, of course, there were the personal computers based on these devices. Given that the 8008 wasn’t introduced until November 1972, the resulting flurry of activity was more than impressive. Only six months later, in May 1973, the Micral was introduced in France. This was the first fully assembled computer based on the 8008, which therefore makes it the first commercial computer based on a microprocessor. Furthermore, the first time the word “microcomputer” appeared in print was in June 1973 in reference to the Micral.
The reason I used the “fully assembled” qualifier with regard to the Micral is that, around the same timeframe, the Scelbi Computer Consulting Company introduced the 8008-based Scelbi-8H microcomputer. Advertised at $565 and equipped with a whopping 1 kilobyte of RAM, the Scelbi-8H was the first microprocessor-based computer kit to hit the market.
In June 1974, Radio Electronics magazine published an article by Jonathan Titus on building a microcomputer called the Mark-8, which, like the Micral and the Scelbi-8H, was based on the 8008 microprocessor. Meanwhile, a guy called Ed Roberts was busily working on his own computer based on the Intel 8080. At some stage, Ed contacted the folks at Popular Electronics in the hope of persuading them to do a cover story on his creation. Not surprisingly, one of the things they wanted to know was the name of the machine. This was a bit of a stumper, because Ed had been so busy on the design that he hadn’t thought to give his computer a name. Ed asked his daughter for a suggestion that sounded “Hi-Tech,” and she responded with Altair, which was the name of a star system in a Star Trek Episode (it was also the scene of the action in the classic 1956 Sci-Fi film Forbidden Planet), and thus was the legendary Altair 8800 born (I have no clue why it wasn’t called the Altair 8080). The resulting do-it-yourself kit was advertised in Popular Electronics magazine in January 1975 for the then unheard-of price of $439. Even better, when the first unit shipped in April of that year, the price had fallen to an amazingly low $375.
In early 1976, MOS Technology introduced the KIM-1 microcomputer, which was based on their own 6502 microprocessor. The KIM-1 boasted 2 K-bytes of ROM (for the monitor program), 1 K-byte of RAM, an octal keypad, a flashing LED display, and a cassette recorder for storing programs. This unit, which was available only in fully assembled form, was initially priced at $245, but this soon fell to an astounding $170. Sometime after the KIM-1 became available, the Sphere Corporation introduced its Sphere 1 kit, which was comprised of a 6800 microprocessor, 4 K-bytes of RAM, a QWERTY keyboard, and a video interface (but no monitor) for $650.
And, of course, in March 1976, two guys called Steve Wozniak and Steve Jobs (who had been fired with enthusiasm by the Altair 8800) finished work on a home-grown 6502-based computer they called the Apple 1 (a few weeks later, on April Fools’ Day, they formed the Apple Computer Company).
Sad to relate, as a student in those days of yore, I couldn’t afford any of the 8-bit computers on the market at that time, which left me wearing my sad face (a little tear is rolling down my cheek and my lower lip is quivering as I pen these words).
We have, of course, wandered off into the weeds (I’m as surprised as you), because none of the above has anything to do with this column, except to say that security in the context of microcomputers was pretty much the last thing on anyone’s mind at that time. Unfortunately, the fact that the vast majority of today’s systems are now connected together in the form of the Internet of Things (IoT) means that security needs to be at the forefront of hardware design and software development.
When it comes to what we now call System-on-Chip (SoC) devices, it’s not so long ago that many of the larger companies spent huge amounts of time, resources, and money designing their own proprietary processor cores. We don’t want to go into the history of Acorn Computers and the Acorn RISC Machine architecture (ARM) here. Similarly, for the purposes of brevity, we will skip over the fact that Acorn Computers eventually spun off a new company called Advanced RISC Machines, which eventually became the ARM (or Arm) company we know and love today. The main point to note here is that the introduction of Arm’s Cortex-M and Cortex-A architectures, which occurred around 16 years ago at the time of this writing, had a huge impact on the industry. Over time, more and more companies dropped their internal processors and opted to use Arm’s processor IP instead. This offered, and continues to offer, a number of advantages, but there is a downside in that — since everyone is using the same processors — there is really nothing left on which to compete except price.
There’s also the fact that the Japanese telecommunications company SoftBank Group acquired Arm in 2016 and is currently trying to sell it to Nvidia, although there is opposition to this deal by a number of players (including Arm China) for a variety of reasons (including national security concerns). Last, but certainly not least, is the fact that Arm leverages healthy license and royalty fees for its IP.
Now, no one is saying that Arm is going anywhere soon, but many users would have preferred it to remain its own company, and its image as a stable entity has certainly taken some dings over the past couple of years. All of which leads us to RISC-V, which is an open standard instruction set architecture (ISA) available under open-source licenses that do not require fees to use.
The creators of the RISC-V hardware concept were inspired by the success of Linux open-source software. RISC-V has a modular design consisting of alternative base parts with added optional extensions. The ISA base and its extensions have been developed in a collective effort between industry, the research community, and educational institutions. Big advantages of RISC-V are software compatibility across multiple implementations, the number of companies offering RISC-V hardware, the availability of open-source operating systems with RISC-V support, and the fact that the instruction set is supported in several popular software toolchains.
For the first six or seven years following its inception circa 2010, RISC-V was rarely seen outside academic circles. By comparison, the past few years have experienced exponential growth in RISC-V processors, devices, and tools. Also, there has been an explosion of semiconductor companies in China that are adopting RISC-V because they want to distance themselves from Arm and/or in response to the American-China trade wars. The chances are that at least one or two of these Chinese companies will become successful enough to compete on the international processor marketplace.
All of this started to make me wonder about security. How do you go about securing your RISC-V-based designs and products as they wend their way through the supply chain? There are myriad stories about companies that create devices that connect to the internet via Wi-Fi to access services and software updates, but that see many more devices appearing online then they ever actually shipped. There are also tales of distributors reverse-engineering designs and selling counterfeit versions based on cheaper components with lower quality. As a result, the company that created the original product is on the receiving end of a double whammy in the form of a nosedive in sales and a compromised reputation (because the purchasers think they bought an original unit and aren’t happy when it fails to perform or dies a death).
In order to sate my curiosity, I reached out to Anders Holmberg, who is the General Manager for the Embedded Development Tools division at IAR Systems, which develops C and C++ compilers, debuggers, and other tools for developing and debugging firmware for 8-, 16-, and 32-bit processors.
I was amazed to discover that IAR Systems was founded in 1983, which is closing in on 40 years ago at the time of this writing. As Anders reminded me, if you look back two or three decades, there were a huge number of compiler companies out there. Over the years, however, some of them went out of business and many of them were bought up by big companies like Motorola and Texas Instruments (it turns out that one of the compiler companies with which I was familiar, Keil, was acquired by Arm in 2005). As a result, there are only a couple of large and trusted independents left, of which IAR Systems stands proud in the crowd.
It may not surprise you to learn that the guys and gals at IAR Systems have security covered. In addition to their flagship IAR Embedded Workbench, which many consider to be the best compiler and debugger toolchain in the industry, they also have a complete security development environment for embedded applications in the form of C-Trust & Embedded Trust .
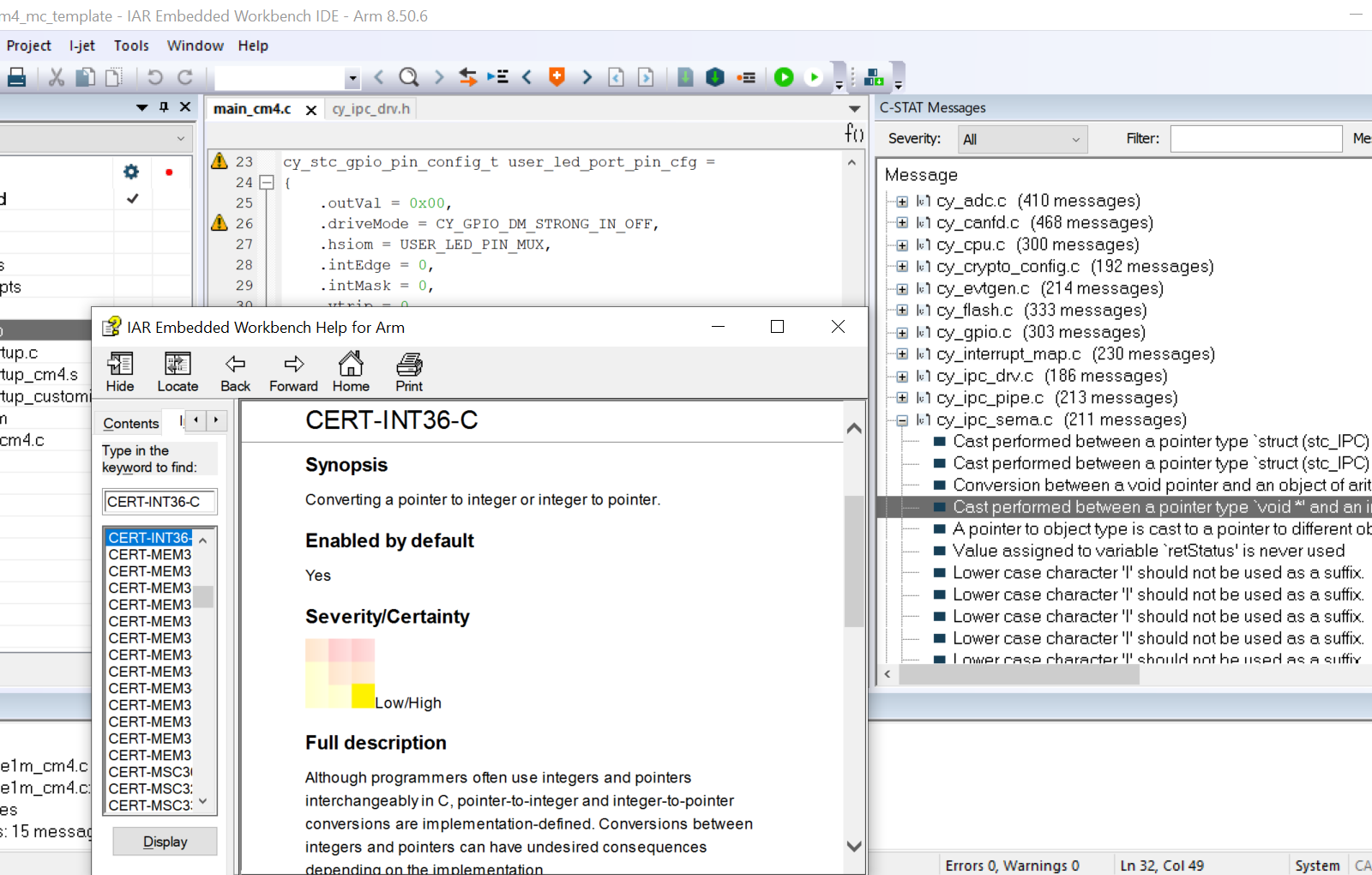
Screenshot of IAR Embedded Workbench (Image source: IAR Systems)
And there’s more, because the chaps and chapesses at IAR Systems also offer the Security from Inception Suite, which provides a straightforward way for their customers to get started with security and build a platform that will extend with evolving security needs, along with their IAR Academy, which offers on-demand, scheduled, or on-site training programs.
The IAR Embedded Workbench toolchain supports more than 30 different processor families including — you guessed it — RISC-V. As Anders noted, “Many in the RISC-V development community are just starting to think about security, and we will be ready to help them when they are ready to be helped.” I don’t know about you, but I have a warm feeling that all is going to be safe and secure in our RISC-V-based future. How about you? Do you have any thoughts you’d care to share?





