As you may imagine, I receive an eye-watering number of emails each and every day. To give you an idea as to the size of the problem: as I pen these words, this is my first day back at work following a four-day break for the Christmas Holiday weekend. I got up at 6:00 a.m. this morning and came straight to my office. I ate lunch at my desk. It turned 3:30 p.m. a few minutes ago. I’ve only now finished wading through the emails that came in over the weekend and just now started writing this column.
There are several reasons why I just regaled you with my email woes, including the (doubtless vain) hope that you will feel sorry for me. More importantly, did you know that — according to a Verizon Business 2019 Data Breach Investigations Report and a Mimecast Threat Intelligence report — 94% of malware is delivered by email; that 90% of file-based attacks use Office files, PDFs, and Archive files; and that 34% involved internal actors behind the attacks?
Obviously, the fact that a lot of malware is made available by email resonates with someone like yours truly who has to meander his way through a lot of emails. Also of interest was a related report from Atlas VPN that slid in front of my eyes a few days ago. This report noted that 19.8% (that’s 1 in 5) of employees clicked on phishing links even after undergoing security training; even worse, 67.5% of these workers willingly gave out their credentials to the phishing site.
It seems like every day brings unwelcome news on the cybersecurity front. For example, unless you’ve been living under a rock, you will be aware of the recent reports of the discovery that Russian state-sponsored hackers have mounted a massive intrusion into US government agencies, private companies, and critical infrastructure entities. All I can say is that these hackers had better not make contact with my dear old mother because she may well be prompted to express some very unkind sentiments that she would doubtless regret later.
With all this talk of doom and gloom, I welcome any little rays of sunshine that come my way. Thus, you can only imagine my surprise and delight a couple of weeks ago when I received an email from one Yehudah Sunshine, who introduced himself as the head of PR for a company called odix.
Yehudah asked me if I would be interested in having a chat with odix CEO Dr. Oren Eytan. Since Oren was the former head of the information security unit of the Israel Defense Forces (IDF) specializing in infrastructure protection, encryption, network security, and mobile devices security, I — of course — jumped at the chance (see also The Rise of International Hacker Networks by Oren).
I have to say that I learned so much from Oren that it made my head spin. Unfortunately, I have to keep consulting my notes to remind me of all the things I’m not allowed to share (it’s for your own safety because if I told you I’d have to send my mother round to visit you).
Let’s start with the fact that odix develops and markets advanced antimalware tools based on Content Disarm and Reconstruction (CDR) technology, which is used to remove potentially malicious code from files. Unlike malware analysis, CDR technology does not attempt to detect or determine the malware’s functionality; instead, it removes all file components that are not approved within the system’s definitions and policies. The easiest way to understand this is by means of a picture as shown below.

High-level view of the CDR process (Image source: odix)
We start with (1) where an innocent-looking file — such as Office, PDF, or Archive — is presented to the system by one means or another. Such a file may include multiple content types, including text, images (some image formats may contain scripts), spreadsheet elements, code, clickable links, and so forth. In (2), the CDR engine scans the file and classifies each content type (I personally think of this as disassembling the file). In (3), we see policy enforcement per file type. Finally, in (4), a malware free file is ensembled in a form that can be safely entered into the system and accessed by the users.
The odix implementation of this technology is called TrueCDR, and the folks at odix have a broad product portfolio based on TrueCDR as the core technology. This portfolio includes odix Kiosk (for sanitizing removable media), odix NetFolder (for sanitizing files in transit), odix Mail Scanner (for sanitizing email attachments), odix Client (a desktop app for sanitizing files on USB appliances), and odix API (for any file processing app).
Take the odix Kiosk, for example. This is something that could be installed at the entrance to any high-security building. If anyone has files on a USB memory stick, they present that stick to the kiosk, which sucks it inside, applies TrueCDR to any files residing on the stick, and presents the user with a brand spanking new stick containing the sanitized files (the original stick is held back in case there is any malware lurking in its low-level firmware).
As an aside, one potential product I think odix should invest in would be a TrueCDR-enhanced QR Scanner app for iOS and Android. I recently saw a LinkedIn post from Alon Golan, who is product marketing manager at odix, saying, “Have you ever thought about malware attacks coming from a QR code? This just in, Malware is everywhere and QR codes are no different.” Eeek, prior to this post I never have thought about this, but now I’m scared to scan a QR code (thanks a bunch Alon).
Unlike legacy anti-malware technologies, odix’s solutions are effective against both known and unknown malware. TrueCDR technology acts as a detection-less method to disarm zero-days and advanced persistent threats (APTs) in files and is considered by leading analysts as an addition (or possible replacement) to existing antimalware technologies.
This is probably a good time to mention that odix is a partner in the Microsoft Intelligent Security Association (MISA), which is an ecosystem of independent software vendors that have integrated their solutions to better defend against a world of increasing threats. All of which leads us to what I believe is destined to become odix’s flagship product, FileWall, which is a native Microsoft 365 security app ensuring complete prevention against unknown attacks delivered through email attachments. FileWall is designed to run in conjunction with existing Microsoft security solutions such as EOP and ATP:
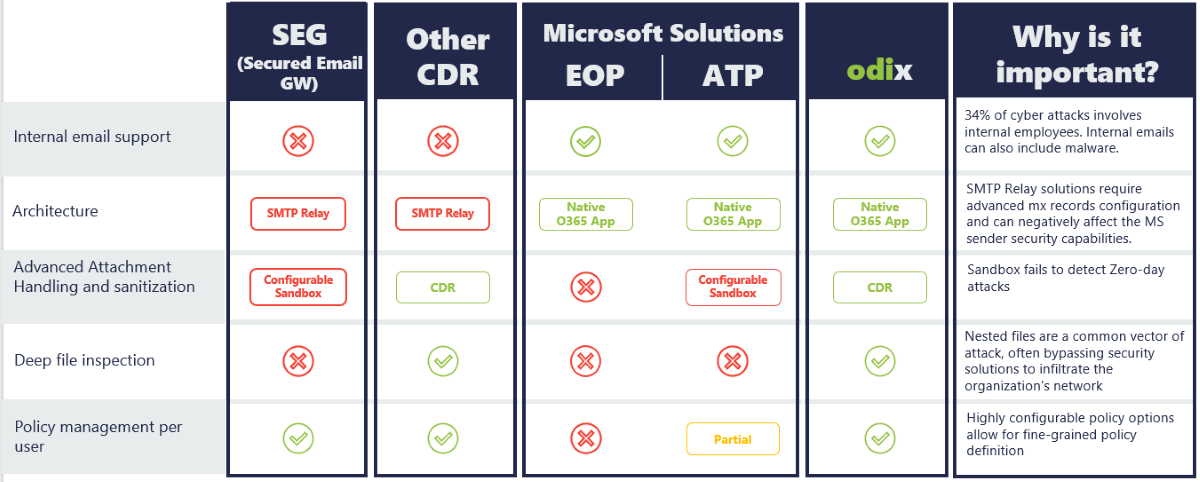
FileWall value proposition (Image source: odix)
Several things jump out at me when I see this figure, such as the row on sandboxes. In the context of cybersecurity, a sandbox is an isolated virtual environment that mimics the end user operating environment. Much like the adverts one might see for a holiday in Las Vegas, the idea is that “what happens in the sandbox stays in the sandbox.” To put this another way, any malware is supposed to be confined to the sandbox and will cease to exist when the sandbox is terminated.
If you’d asked me before my chat with Oren, I would have said that sandboxes were the cybersecurity solution to life, the universe, and everything, so you can only imagine my disillusionment to discover that they fail to detect zero-day attacks. Even though it’s just an image, I find the green CDR box on the sandbox row in the odix column in the above illustration to be strangely comforting. I also like the fact that FileWall provides deep file inspection, thereby reaching any malware hidden deep within attachments, including malicious code hidden in embedded files and archives.
I just watched this When Jane met FileWall video, which sums things up in a nutshell. I have to say that, although the IT guy, Jeff, is the hero of this piece, the creators of the video have really nailed his supercilious laid-back “I know all things and you are not worthy of my attention” look (not that I’m bitter, you understand).
The main takeaway from this video is that, with a single click deployment, the folks in IT can provide malware and ransomware prevention for M365 Exchange Online — all they have to do is visit the FileWall for Exchange Online page in the Microsoft App store and click the “Get it Now” button to perform their magic. At only $1.00/user/month, I would say this is a “must have.”
Speaking of which, even though I’m only an organization of one, I’m going to see if I can get this for myself. I do try to be careful, asking “did you actually send this” to everyone, including close friends, if something unexpected comes in, but even if they reply “yes,” there’s no guarantee that something unpleasant isn’t buried deep within.
I used to laugh at the saying, “just because you’re paranoid doesn’t mean the b######s* aren’t out to get you” (*naughty people), but my laughter is starting to ring a little hollow these days. How about you? Are you starting to become paranoid like me?