The developed world – particularly the US – is a complex environment replete with residents from diverse places and backgrounds with widely differing experiences. But it’s not a homogeneous mix: cities will be more diverse than rural areas, and, even within cities, you’re going to get clusters of people with shared characteristics.
Well, there appears to be a cluster of people – not sure where – that have the following traits:
- They’ve lived in one place, and they went to one set of schools.
- They’ve had one set of friends for their entire life.
- They have clear favorites of everything. And those favorites never change, ever. By the time they’re 25, they have a favorite pet, movie, book, teacher, TV show, musician, song, everything. And even though they have 60 years ahead of them, those favorites will stick.
Who are these people? They’re the ones deciding the challenge questions for your secure log-in. The questions are mostly used for confirmation that you’re who you say you are if you need to change your password or do some other ultra-privileged thing.
Other sites use them more intrusively. With my credit union, if I log out and then log back in again within an hour (or some period), it wants confirmation that I’m still me. Or at random other times when trying to do something, it will interfere with a challenge question even though I’ve checked that box saying, “Yes, this is still my private computer, just like it was 10 minutes ago. No, I’m not being burgled.”
In theory, this would seem to be a reasonable idea. If you want to prove that you’re you, then provide some information that only you would know. It sounds good up until you’re provided with the opportunity to set up your personal questions and answers. That’s when the trouble starts.
I don’t want to come across like some emo goth who’s simply too complex to have his essence captured and reduced to three banal questions. But I always tense up when the time comes to find my personal questions: will I be able to find three with unambiguous, lasting, memorable answers? I always come away feeling like the question-selectors came from some small-town cluster where everyone was the same and life was uncomplicated by complex options.
You might as well have questions like,
- What’s your favorite model of Mercedes?
- Which is your favorite Shoney’s?
- Who makes the best hot dish?
- What’s your favorite breed of cattle?
If you’re not in a suitable population cluster from the Bay Area or Connecticut or the South or Minnesota or Nebraska or Texas, you’re not likely to find a suitable question in that mix.
There are three main weaknesses to most of the options.
- They don’t reflect your life. “What’s your spouse’s favorite color?” – when you’re not married.
- You can find a question for which you have a definite answer at that moment, but the answer will change according to your mood or after you read a book that’s even better than your last fave.
- You don’t have an obvious answer, so you have to just pick one – and you may not remember your random selection when you need it.
For any individual, any given question might be irrelevant, of course, and so there’s a selection of questions – with the expectation that everyone will be able to find three that work. But each time, I barely skate by with three questions that I can use, and I’ve wondered when the time would come that I couldn’t find three questions with unambiguous answers.
My luck finally ran out the other day when an airline for which I’m a frequent flier – or, rather, used to be a frequent flier – suddenly needed me to upgrade my security. (As always, these things are “URGENT, MOST DO IMMEDIATELY!”) And this time there was a twist: no more having to come up with answers. They provided not only the question options, but the answer options too.
So even if I could find a question with a solid answer, if it wasn’t one of the answers they offered up, it wouldn’t work. And I needed not 3, but 5 questions. And each question drew from the same list (some sites have a different list for each question). It’s like their IT department got spanked for lax security and said, “OK, you want tight? I’ll give ya tight!” For the first time ever, I aborted the process.
I have to say, they did do some work trying to come up with exhaustive answer lists. Here are the questions:
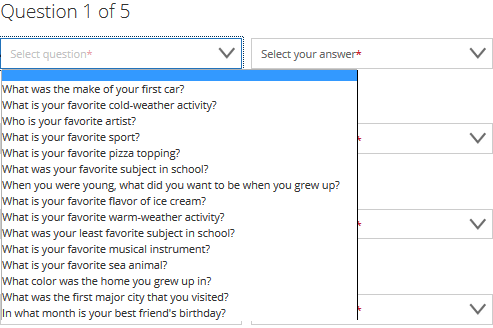
Heavy on the favorites (something that doesn’t do well for me because of that changing-with-mood-and-context thing. My favorite kind of food, for example, depends on whether I’m in Boston, Austin, or San Francisco).
If we look into the first question, it’s pretty unambiguous: we all had a first car. Unless, that is, we’ve never had a car. Yes, there are people leading totally carless lives. The list of automobile options is pretty extensive; I don’t know if everything is there, but this is one question I could go with.
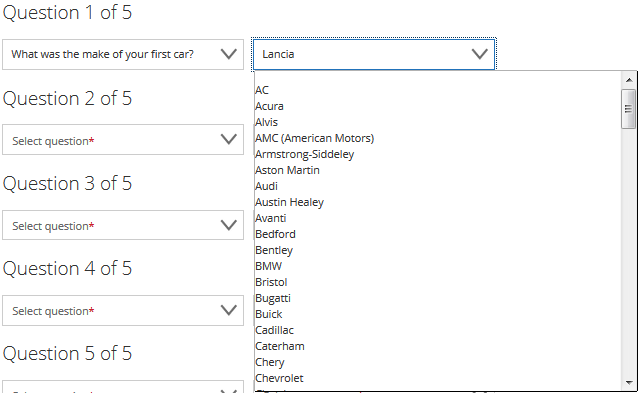
(And no, I don’t have a Lancia.)
But what about the career dreams of children?
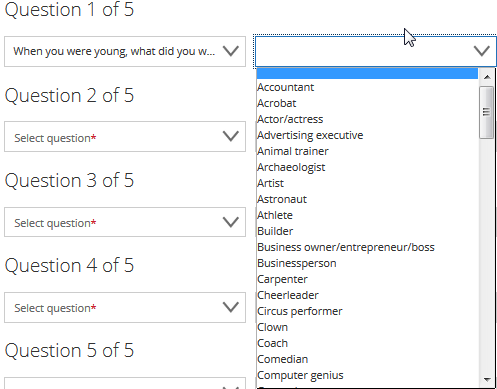
Really? Kids grow up dreaming of being ad execs? Go Mad Men! But what if I grew up wanting to be a bounty hunter? Or a bail bondsman? Not on the list… no can do.
Heck, I can just see it now:
- What’s your mother’s maiden name?
- Smith
- Andrews
- Jones
- Taylor
- [other Anglo names]
Up to this point, this is just me snarking and whining about how I’m too special to submit to such simplistic questions (and answers). But I’ve always thought there’s a better way to do this, even when you have only a question list to pick from. Even more so when you get an answer list as well.
If the whole idea here is to identify something that only you know uniquely, then the best questions and answers would be uncommon – ones that would not likely be on anyone’s list of obvious questions and answers.
I don’t specifically know how these things are stored, but if someone can hack the question options, then they’re part way to breaking the security. If they can now also hack the answer options, then they can, in theory, brute force their way through the answers until one works. A sophisticated system would notice such behavior, but are these systems sophisticated?
As it is, an intruder can learn the candidate questions (and answers) by creating a bogus account and capturing all of the question (and answer) options. From there, a determined soul could do some research about a target individual, toss in a dash of trial and error, and doors might open. That may not be a high-volume break-in, but it’s still a break-in. (And the low volume thing might reflect only my limited imagination.)
Here’s a better way: let us come up with our own questions and answers. I can’t say what my favorite pet was, but I can answer definitively, “What was the name of your pet that consistently pooped under the piano when you were around 9 years old?” Funny… I’ve never seen that question on any list.
And that’s just the point. If a would-be intruder has absolutely no knowledge of what the questions are going to be (much less the answers), then it’s going to be even less likely that they can break in. Granted, the way these work, you’re presented with a question, so, on the surface, hacking a question might not be an issue. Then again, I’m not a hacker, and I’m constantly amazed at the indirect and unobvious ways people break into things. Apparently, security folks are similarly amazed (as they rush to patch unobvious vulnerabilities).
I’ve actually thought this for years, but I wasn’t spurred to action (if you can call writing a rant “action”) until the answer list thing reared its head. And some of those thoughts consisted of wondering why the create-your-own-question thing wasn’t an obvious solution.
The only thing I’ve been able to come up with is that, with pick lists, you can store the answers as indexes. I don’t know if that’s how it’s done, but, since that uses little memory, you could envision that being the answer.
Saving a created question, of course, requires storing – and hashing – all that text. But in an era of big data, that amount of data officially qualifies as mice n…oses.
There is one possible other reason: perhaps lots of people don’t want to think hard enough to come up with questions. So, to cover this case, you could have a list of pre-canned questions with a “create your own” option at the end for those of us unsatisfied with our selections. Kind of like a pizza menu.
I don’t know if there’s some other barrier (please feel free to answer in comments if there’s more to this); seems pretty straightforward to me. I’ll even trot out the five deadliest words in business: “How hard can it be?”
OK, so I’ve finally gotten this off my chest. Have you had similar experiences? Do you belong to a population cluster that’s poorly represented in challenge questions? What’s your favorite challenge question? (Oo! Oo! That should be a challenge question! It’s so meta!) If you have some good challenge question stories, please do share them with us in the comments.






Do you have any good challenge-question stories?